“It isn’t going to happen to me. I am just a small business on the Western
Slope.” This is a narrative that many businesses tell themselves every day regarding cyber-attacks, more specifically, ransomware. The fact is, if you are connected to the internet, you are at risk.
The media has done many of us a disservice by focusing on the big brands and large attacks with little mention of the thousands of other victims. For every Colonial Pipeline attack, there are hundreds, if not thousands, of other businesses that are impacted by cyber-attacks and ransomware.
Ransomware is a specific type of cyber-attack where the attackers first take a copy of your critical business data and then make all of your files inaccessible to you through encryption. They leave behind a ransom note, typically a text file, with instructions on how to engage and pay them to not
release the stolen data publicly, and to allow you to access your files again. I have seen first-hand how this can end a business. Impacted organizations can no longer make payroll, ship products, communicate with business partners. It impacts operations, financials, and can have a tremendous brand and public relations impact.
Ransomware is not a new phenomenon; some variations of this attack have existed since the 1980s. In those days the attackers used floppy disks mailed to the victims that when inserted into the drive, the disk had a virus that would lock all the files and demand that a money order be sent to a PO Box in a Latin country. The proliferation and increased volume of ransomware has primarily been driven by cryptocurrency technology, the dark web, and
poor security practices by business owners. Cryptocurrency provides an anonymous method of transferring large amounts of capital across international borders almost instantaneously. The Dark Web provides an anonymous method of communicating and facilitating illegal activity. Businesses, who are rapidly leveraging technology, do not fully understand the risks of that technology to their business.
I have spent the last couple years working on ransomware response cases for both large and small businesses all over the world. You can see a detailed review of how I became involved here: https://www.newyorker.com/magazine/2021/06/07/how-to-negotiate-with-ransomware-hackers
Most ransomware attackers are based out of eastern European countries or in Russia where they are offered amnesty for their actions as long as they are not targeting Russian assets. This allows these attackers to act with impunity without fear of reciprocity or consequences. This provides the attackers a tremendous amount of leverage against their victims.
It would seem businesses are at a disadvantage; how can we stop this?
To stop ransomware, we must look inward and better protect ourselves from attack. The cyber criminals are running an operation similar to a business. They look at effort, time, and capital investment on an attack and seek to drive a return on investment (ROI). The key to minimizing your risk, is to become too expensive a target. (e.g. do not be the “low hanging fruit”.)
Ransomware: It won’t happen to me
Each ransomware case that I have been involved in, myself and my team take inventory on how the cyber criminals gained access to the victim. Many, many cases later, we have distilled that list down to a small number of “cyber hygiene” items that businesses can employ to reduce their risk of being a victim significantly.
Some simple steps a company, of any size, can take to protect themselves include:
- Better password policy and business credential use / policy\
- Multi-factor authentication (MFA)
- Email security and anti-phishing software
- User training
Patching systems
I recommend using a password manager program to assist in better password hygiene. There are many options available and most have a business license that allows companies to govern those rules. Multifactor should be used everywhere possible, but especially when remotely accessing the network, and in email systems. Of course, we all know not to click on the links in emails from strangers. Unfortunately, the cybercriminals have become more clever and often those messages appear to come from people we know or even inside the company. Having a software solution to help you identify and flag these attacks is critical. Further, education fixes much of the behavioral problem. Have a security training program for your staff. Finally, update your systems, your phones, your point-of-sale kiosks as often as possible. You can access a more comprehensive list here: https://www.groupsense.io/tips-to-better-protect-your-data-from-ransomware
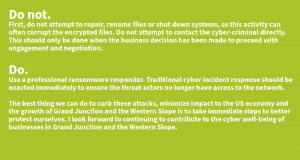
If the unfortunate should happen and you find yourself victim of a ransomware attack: